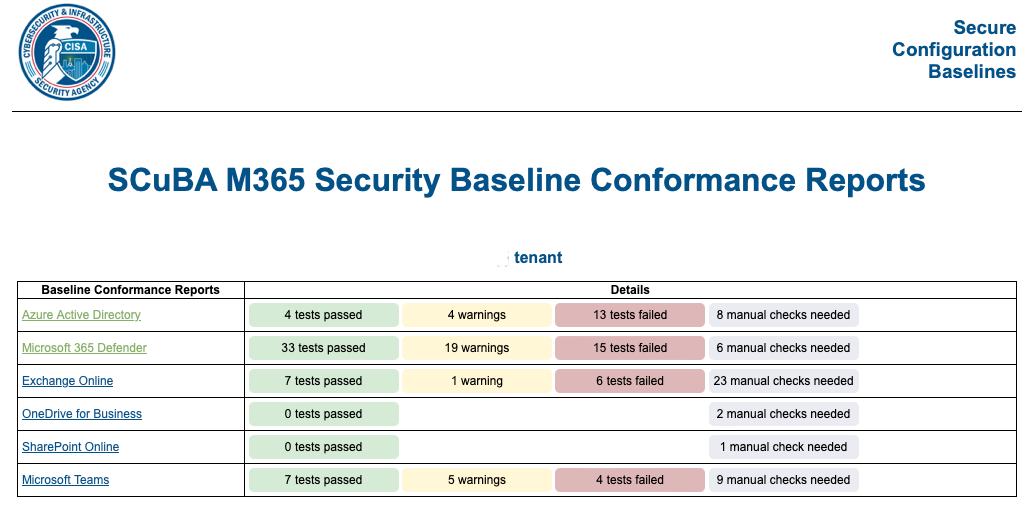
Secure Cloud Business Applications – assess your security
Read More: Secure Cloud Business Applications – assess your securitySecure Cloud Business Applications, assess your security – Best of all it is at no cost and provides guidance on best practise security guidelines for business. When reducing the likelihood of a successful cyber attack we need to break down the approach into various elements, a security assessment such as the CISA SCUBA tool is…
Protecting Australian Business from Cyber Crime
Read More: Protecting Australian Business from Cyber CrimeProtecting Australian Business from Cyber Crime, easy title to write and a topic beyond complex to implement for many small to mid sized businesses in 2022, Australia. The secret is that it is not complex to get started on a cyber security journey, it is easy to do the basics and reduce the risk of…
As Secure As Practical (ASAP)
Read More: As Secure As Practical (ASAP)As Secure As Practical (ASAP) – As Soon As Possible. In the past few months of 2022 in Australia alone there have been a number of significant cyber breaches across many of our major brand names and this terrible trend is poised to continue to get worse until such time as our organisations uplift their…
Threat and Vulnerability management
Read More: Threat and Vulnerability managementThreat and Vulnerability management, an absolutely essential part of security for your organisation. Though my dislike for statistics is known, SIXTY percent of breaches are claimed to be from unpatched software and though statistics may be guided by the authorising (paying) agency/vendor, it does not change the underlying seriousness that we all face with keeping…
Michael Brooke presents the ASD essential 8 on Safari
Read More: Michael Brooke presents the ASD essential 8 on SafariMichael Brooke presents the ASD essential 8 on Safari; recently I had the opportunity to work with TechforGood, an organisation making a difference with Social organisations across Australia. I have two passions other than fishing and family (so four passions in total), these are: Cyber security, the field of cyber security is an industry where…
Carrots, sticks and Donkeys do improve cyber security, part 1
Read More: Carrots, sticks and Donkeys do improve cyber security, part 1Carrots, sticks and donkeys do improve cyber security, part 1. More specifically how to Use the ACSC recommendations to achieve cyber resilience augmented with what organisations are already doing well today. As most organisations in Australia already understand, the Australian Signals directorate Essential Eight is a list of 8, easy (definitely easy) steps to implement…
Machine learning – hype or hope with 1 part snake oil
Read More: Machine learning – hype or hope with 1 part snake oilMachine learning – hype or hope with 1 part snake oil, adding the snake oil makes all things including Machine Learning more capable than it may seem when peeking beneath the covers, or more slippery, but we will get into the slipperiness soon. The following article is something that I have wanted to write for…
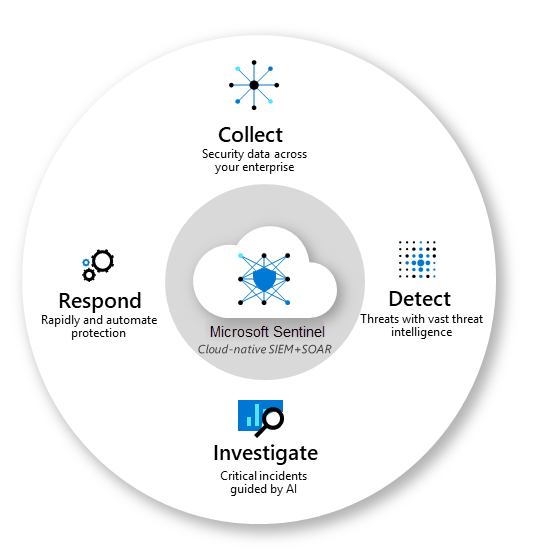
#1, Down and Dusty with Microsoft sentinel
Read More: #1, Down and Dusty with Microsoft sentinel#1, down and Dusty with Microsoft Sentinel. Sentinel is one of Microsofts Crown Jewels hidden so well in plain sight that many Managed Service Providers and cyber security teams do not even know it can help them significantly with investigating Indicators of Compromise or investigating a cyber attack to find the source and the target.…
Protection before Detection – Endpoint detection response
Read More: Protection before Detection – Endpoint detection responseProtection before Detection – Endpoint detection response Endpoint Detection and response gets a lot of attention from the entire cyber security industry, EDR as it is commonly known is a valuable tool in a corporate kitbag, but is Endpoint and response something that should be acquired first, second or where? If we review the Australian…
0-day Atlassian Confluence vulnerability, no patch yet
Read More: 0-day Atlassian Confluence vulnerability, no patch yet0-day Atlassian Confluence vulnerability, no patch yet. Known as CVE-2022-26134 it was acknowledged by the Atlassian team on the 31st May 2022. Update 04/06/2022: patch for the Atlassian Zero day is available here. A quick google search for “Confluence wiki”, CSIRO pops up an already disabled confluence site, any attacker has much more capable tools…