Protection before Detection – Endpoint detection response
Endpoint Detection and response gets a lot of attention from the entire cyber security industry, EDR as it is commonly known is a valuable tool in a corporate kitbag, but is Endpoint and response something that should be acquired first, second or where?
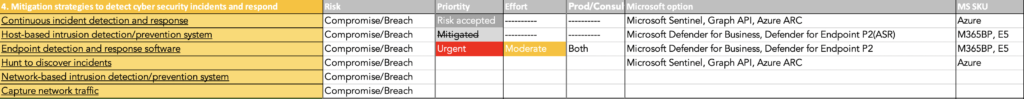
If we review the Australian cyber security centre security mitigations, endpoint detection and response or EDR is not an essential 8 control and for very supportable reasons, but is it a control to have in place for all organisations, where in the order of cyber security controls should Endpoint detection and response be included?
The answer is not straightforward and we will get into it with our dive into the subject for today ”Protection before Detection – Endpoint detection and response”
Cyber criminals are often still using the same tools as they were 4 years ago. This article linked here, shows just how much things change in the hacking world, but yet stay the same.
Malicious actors are still using the same tools to attack business
In terms of the tools and methods that ransomware actors use, Cobalt Strike is common for interactive sessions, RDP for lateral movement, Mimikatz and LSASS dump for credentials, and SMB + WMIC and Psexec are typically usd for deploying payloads on the network hosts.
Bleeping computer
Protection before Detection?
With all things in life there is an order in which we “should” undertake to achieve the best result, especially when referring to attacks or criminal activities such as theft or arson which is where many cyber crimes appear. Or the burglar alarm in your home when there are no locks on the back door.
Just as at home, stopping a cyber breach in the first instance is cheaper, faster and easier than trying to recover a business that is unable to operate due to a Ransomware attack.
Protect

Specifically referring to crime, protection is the only way to ensure that your valuables are safe. Protections must be put in place first for this very reason, stopping an attack whether physical crime or cyber attack is what your security team needs to be focused on first.
Preventing a cyber breach or data breach is of primary importance to any business, you see once the data is encrypted or exfiltrated, it does not matter if an EDR was able to pick up an attack underway, it is too late by this stage your data is already gone.
As mentioned in the first paragraph, most cyber attacks follow a common path for opportunistic cyber attacks, looking at the scenario from a protection standpoint you can prevent these attacks from being successful following the Australian Cyber Security Centre ASD essential 8 – thereby mitigating most of your risk by 85% according to the ACSC themselves.
An Ounce of protection is worth a pound of cure
Merriam-Webster (and my dad)
Cyber criminals are ‘crafty’, they do not work like you or I. They have one job to do and that is to infiltrate your network and cause you havoc and pain – a specialist criminal is always better than a generalist cyber security analyst so removing the ability for an attacker to operate is critical to your defence.
Detect

Detection capabilities are a follow up technology, detecting that a crime has been committed is fraught with challenges, firstly: did the criminal “turn off the detection capability”?, did the criminal do something new that has never been seen before, is the attacker doing something in a way that is like a normal user would do, did the attacker pay an employee to give them their credentials as per Lapsus$ which I wrote about here.
Where as detection of breach capability is an additive technology, it is a Reactive cyber security posture and not a proactive posture which involves actively preventing your business assets from being stolen in the first place.
My analogy for detection is watching your almost new 85 inch OLED television drive off down the street; you detected the TV is leaving but it is too late to stop it.
If you have endpoint detection and response in place already then the software is of huge value with the right operators managing the alerts, because the foundation of cyber security is defence in depth and layering protection/detection solutions ensures that your organisation is as secure as it can be expected to be.
If you are not invested in Endpoint detection and response software yet, then please read on….
Protection before Detection
Now that my reading audience has now reduced with EDR peps leaving the ‘room’, I want to let those who remain in on a few tricks and tips that may save you some capital and avoid some painpoints from the Board of directors when there is a breach and they assume that the Endpoint detection and response technology should have stopped the attack – EDR may have stopped it, but then the next attack came from a different approach as previously discussed.
- Endpoint detection and response solutions are not an ASD Essential 8 control and for very good reason, the Australian Cyber Security Centre knows that protection of assets is the most important control that businesses can put in place for their protection. By focusing on the Essential 8 first you reduce the risk of a cyber breach by 85%
- Here is an example of avoiding EDR, just read here to understand just how easy it is to find a way to obtain persistence on a Crowdstrike protected network, this extends to all EDRs including Microsoft Defender for Endpoint P2 – Microsoft Defender for Endpoint P2 has a secret little trick that places it ahead of other EDR solutions, which I will mention below.
- When reviewing EDR choose one that has protection capabilities as well, such as Microsoft Defender for Endpoint P2, or the very affordable Defender for Business as these solutions also help with 6 of the ASD essential 8 controls.
- Look at application control technologies, Products like Airlock Digital focus specifically on allowing only the standard and necessary applications the ability to run and block all others, with capabilities such as One Time Passcode overrides for special cases and certificate trust so that updates can run.
- Application control will completely remove the opportunity for malware to be able to execute altogether.
- Attack surface reduction, capability built into Microsoft Defender for Endpoint P2 (Business) is also capable of preventing 0 days attacks such as Follina. Attack surface reduction must be enabled though and the settings applied.
Protection before Detection summary
The ACSC ASD Essential 8 is about protecting businesses first. Always look to protect your assets first and foremost, data and access to that data is your lifeblood and the difference between having a business and not being able to continue trading.
The debate about protection vs detection can be an emotional one, there are cyber security professionals who sip the EDR coolaid, the intent of this article is not to say they are wrong, but simply to apply logic to the argument, Protection is better than detection until a business has adequate protection in place and for Australian Businesses who do not have the ASD Essential 8 in hand – achieve the Essential 8 first.
Please leave any comments or feel free to reach out to us here for further information.




