Anthropic Security Agents will change the Managed Security Operations game forever
Read More: Anthropic Security Agents will change the Managed Security Operations game foreverAnthropic Security Agents will change the Managed Security Operations game forever. Anthropic just dropped a MDR / Managed SOC bomb that looks like it is the real deal, causing an immediate stock price drop across the major cyber security companies globally, arguably more of a “true up” than a valuation change as it is the…
Avoiding a Global outage – By not running the software that caused it!
Read More: Avoiding a Global outage – By not running the software that caused it!Avoiding a Global outage – By not running the software that caused it! In a article this morning ABC journalism competently managed to demonstrate a complete lack of awareness in the topic they were reporting on and a media story was born that has no basis to even exist in this reality, or the next.…
Ticketmaster – When a third party supplier breach is not what it appears
Read More: Ticketmaster – When a third party supplier breach is not what it appearsTicketmaster – When a third party supplier breach is not what it appears. As many of us learnt whilst growing up, most of the time obfuscating facts to portrait yourself in a brighter light actually creates a bigger problem. Now as an adult I am not going to have my parents tell me off but…
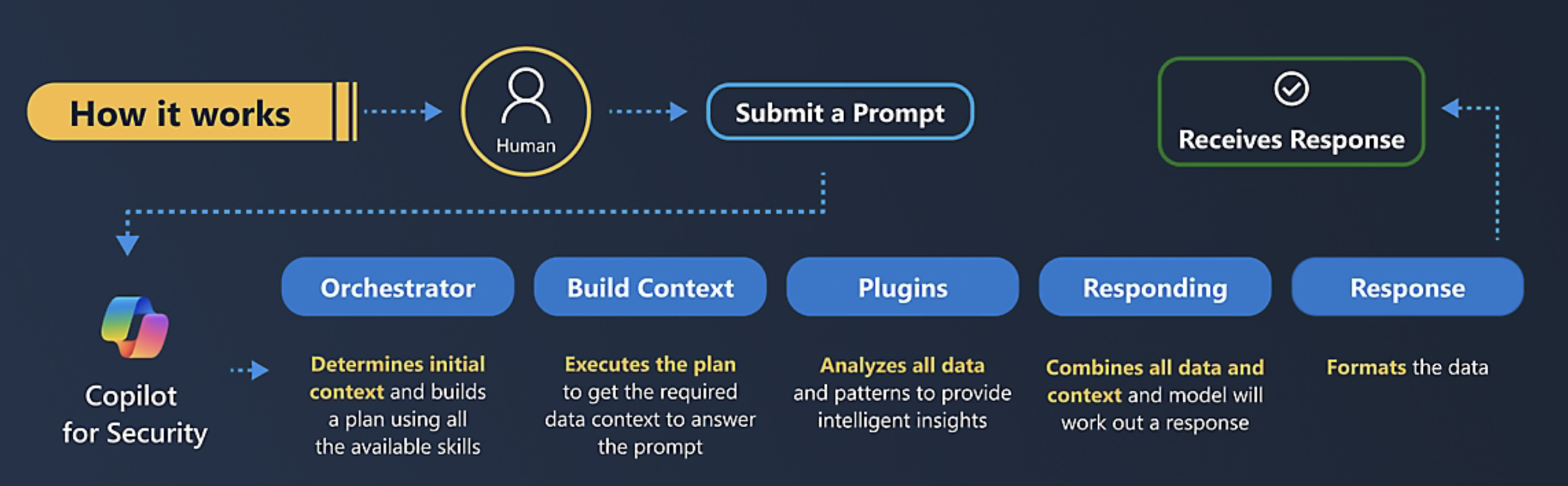
Microsoft Copilot for Security Ninja Now operating and at your service!
Read More: Microsoft Copilot for Security Ninja Now operating and at your service!Microsoft Copilot for Security Ninja Now operating and at your service I recently completed my Microsoft Copilot for Security Ninja training, now I’m ready for those Security copilot conversations with Partners and customers….. of course this is not true! I am but a mere amateur. I do have the ‘certificate’ but I am no expert…
Sugar And Statistics, sprinkles of nothingness
Read More: Sugar And Statistics, sprinkles of nothingnessSugar And Statistics, sprinkles of nothingness: Last night I went fishing in our new boat and we caught 2 Dusky Flatheads, ugly but a great eating fish, sorry I digress but it seemed important at the time, here they are – we had no time to name them: Sorry I got distracted (a challenge with…
Consulting Integrity
Read More: Consulting IntegrityConsulting with Integrity is critically important in my industry of Cyber Security, there are many consultants preaching to be what they are not, “knowledgeable” people. The Cyber security industry is fully of vendors and sellers trying to position security tooling as a solution to a cyber risk problem. I want to share a recent story…
Occams razor – When an attack is unknown?
Read More: Occams razor – When an attack is unknown?Occams razor – When an attack is unknown? This is a true story with a recent Managed Service Providers customer: Customer was breached, bank account details changed and a significant amount of money was transferred from the business account. I am not using industry or amounts to keep this anonymous, this tale though illustrates something…
Splunk, assassinated by Cisco – RIP
Read More: Splunk, assassinated by Cisco – RIPCisco to acquire Splunk? good news? not if you are a Splunk customer, not if you are a Cisco customer either….. Splunk was one of those brands that I could not get my head around, a name that seemingly means nothing to Americans but to others on the global stage, almost dirty but not quite.…
Supply Chain risk
Read More: Supply Chain riskThere has been a number of supply chain attacks recently including MoveIT and 3CX, these cyber attacks can be immensely costly and at the lest distressing for the businesses involved. For the software provider though these breaches can and often do have disastrous impact on their business, which could have been avoided by following a…
From Backup to resilient cyber security
Read More: From Backup to resilient cyber securityIn the Beginning From Backup to resilient cyber security: Best practises for Information Technology such as “Least privilege access”, “Admin account segregation”, “Operating system patching”, “Multi-factor authentication”, even “Patching and updating applications” have been around for many years, undertaken as ritual by many Information Technology departments within businesses across Australia as best practise maintainence, without…