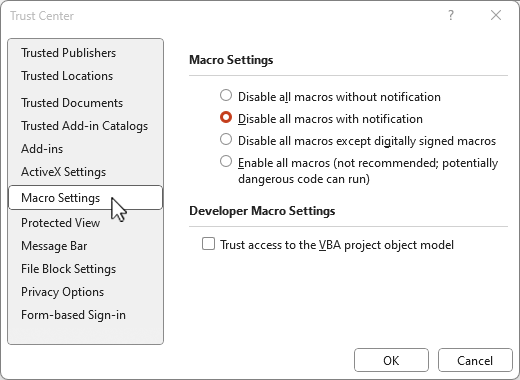
Microsoft Office Macro security – Are you covered?
Read More: Microsoft Office Macro security – Are you covered?Microsoft Office Macro security – are you covered? Microsoft Office macros are an amazing way to automate and script many parts of a business process, sometimes directly on an Office document, Spreadsheet or PowerPoint but also for interacting with third party data, the operating system and more, which is also why the recommendation today in…
Protecting Australian Business from Cyber Crime
Read More: Protecting Australian Business from Cyber CrimeProtecting Australian Business from Cyber Crime, easy title to write and a topic beyond complex to implement for many small to mid sized businesses in 2022, Australia. The secret is that it is not complex to get started on a cyber security journey, it is easy to do the basics and reduce the risk of…
As Secure As Practical (ASAP)
Read More: As Secure As Practical (ASAP)As Secure As Practical (ASAP) – As Soon As Possible. In the past few months of 2022 in Australia alone there have been a number of significant cyber breaches across many of our major brand names and this terrible trend is poised to continue to get worse until such time as our organisations uplift their…
“Okta parses passwords in clear text”, What does that mean to me?
Read More: “Okta parses passwords in clear text”, What does that mean to me?“Okta parses passwords in clear text”, What does that mean to me? This is really NOT an Okta problem but an industry problem – my industry, cloud SSO authentication should always and only be against known “good” Authenticators such as Microsoft, Google, Apple and others for all cloud based SSO. Passwords should never be out…
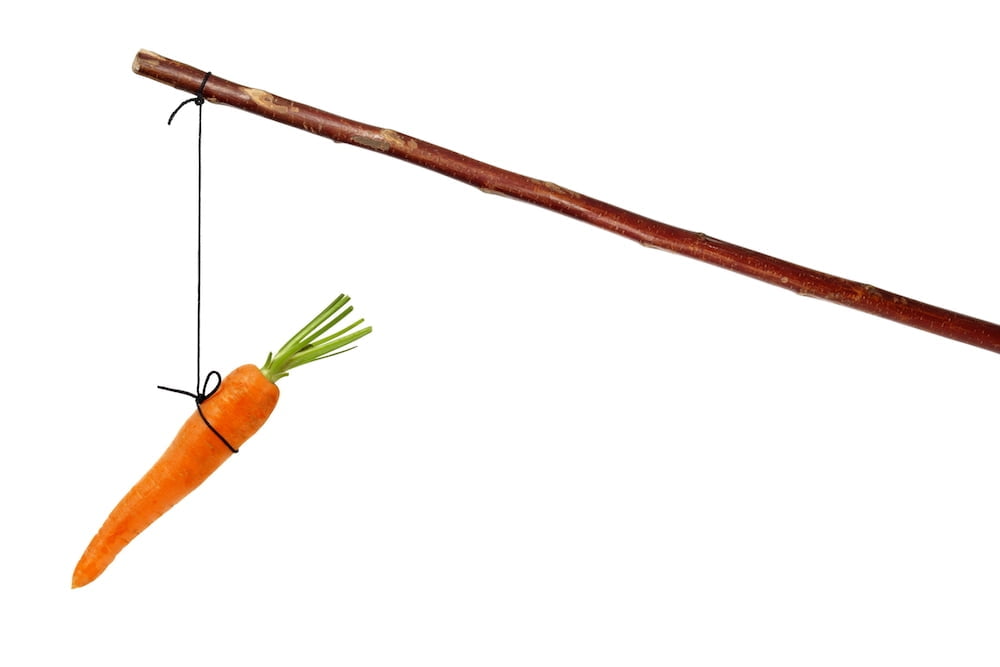
Carrots, sticks and Donkeys do improve cyber security, part 1
Read More: Carrots, sticks and Donkeys do improve cyber security, part 1Carrots, sticks and donkeys do improve cyber security, part 1. More specifically how to Use the ACSC recommendations to achieve cyber resilience augmented with what organisations are already doing well today. As most organisations in Australia already understand, the Australian Signals directorate Essential Eight is a list of 8, easy (definitely easy) steps to implement…
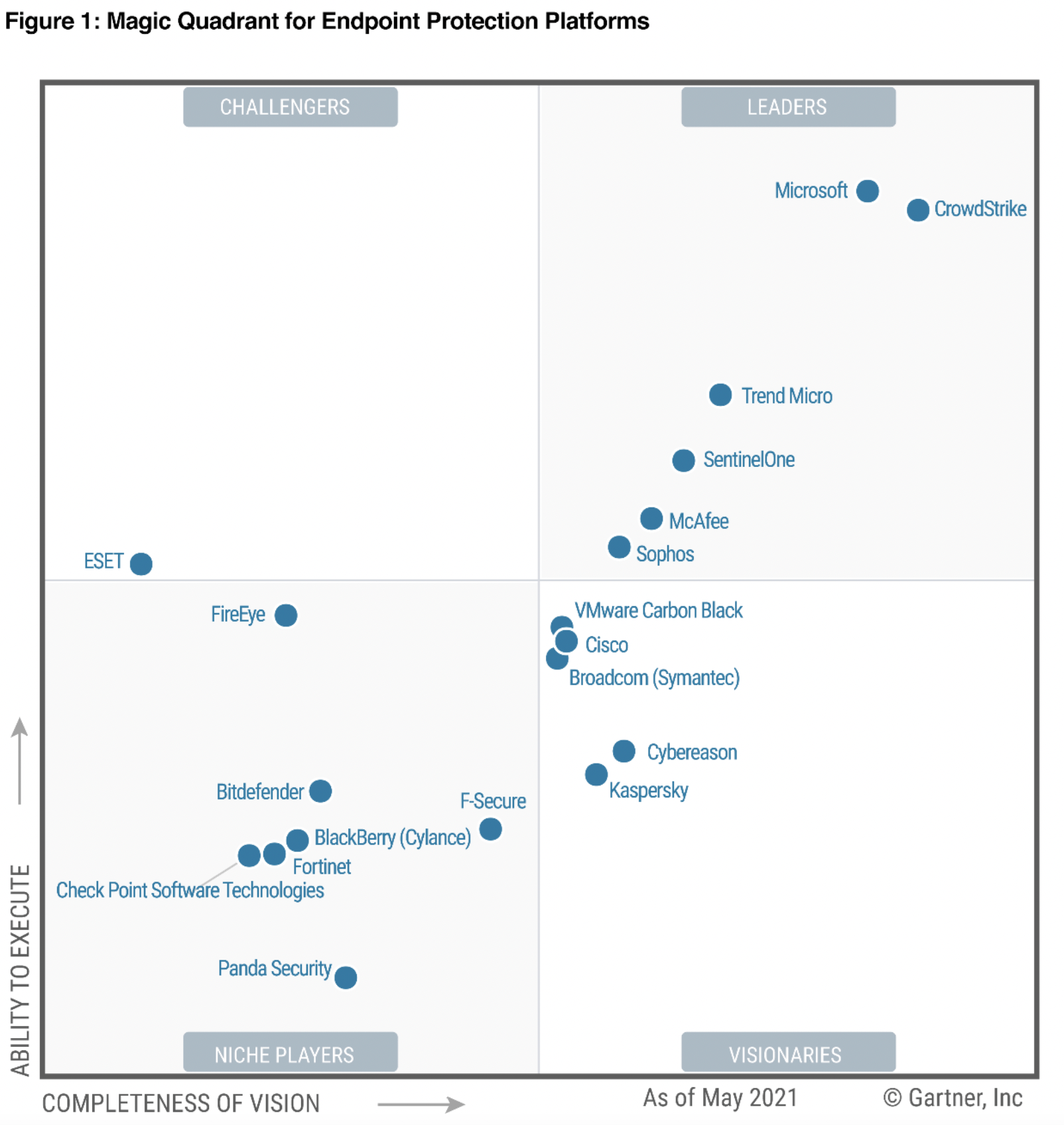
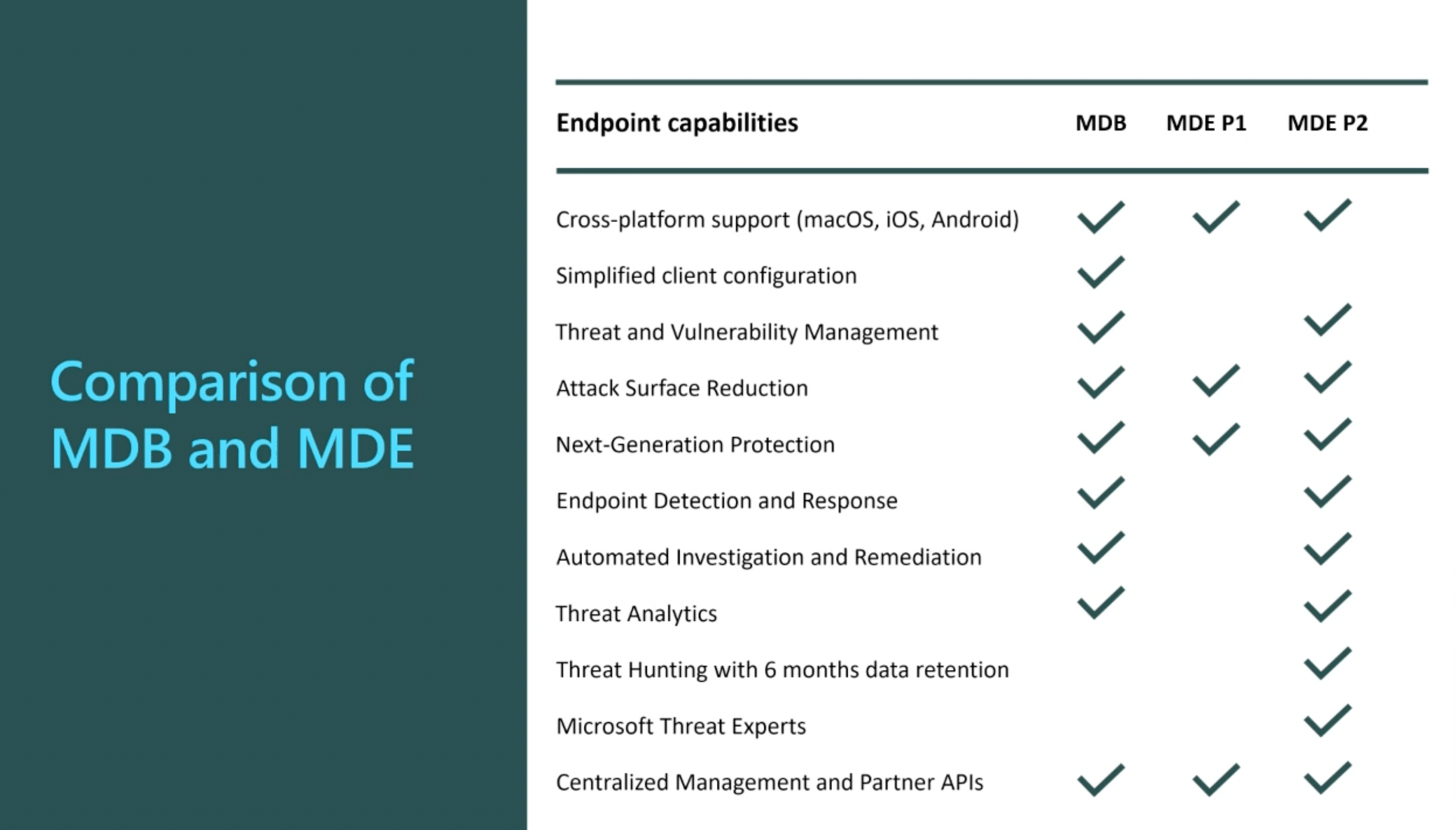
The No.1 way to protect Data, Defender for Business and Premium
Read More: The No.1 way to protect Data, Defender for Business and PremiumThe No.1 way to protect Data, Defender for Business and Premium, MSP’s and businesses looking for better coverage of the ASD Essential 8 with the fewest possible products should look at Microsoft Defender for Business or Business Premium preferably. This morning a colleague (thanks Ross) sent me this article and it reminded me that we…
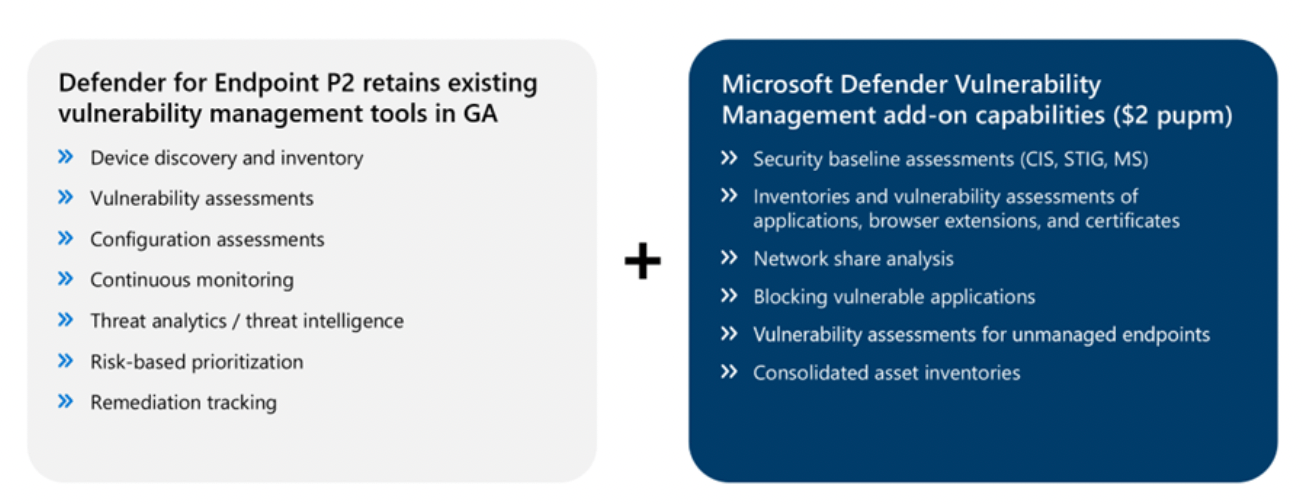
Microsoft Defender vulnerability Management dropping shortly
Read More: Microsoft Defender vulnerability Management dropping shortlyMicrosoft Defender Vulnerability Management dropping shortly for customers as an add-on for Microsoft Defender for Endpoint P2 or a standalone license. Vulnerability assessments and Management of these vulnerabilities has been missing from the Microsoft stable and this is a great addition for customers as it brings the element of protection to what was previously only…
Microsoft Defender for Endpoint training resources
Read More: Microsoft Defender for Endpoint training resourcesMicrosoft Defender for Endpoint training resources: The goal of this page is to put together a level 101/201 resource for consultants and end customers to utilise to find out more about Defender for Endpoints, I will update the details as they change but this is current as of May 2022. Microsoft Defender for Endpoint training…
Once the horse has bolted – or detection and response should not be an early stage cyber resilience control
Read More: Once the horse has bolted – or detection and response should not be an early stage cyber resilience controlOr in other words detection and response solutions should not be a first step in a cyber resilience strategy – after the horse has bolted is too late to be worried about how the animal got out of the stable. The Australian Cyber Security Centre does not even list Endpoint detection and Response solutions in…
Microsoft Autopatch – Patch Tuesday is gone for good!
Read More: Microsoft Autopatch – Patch Tuesday is gone for good!Microsoft Autopatch – Patch Tuesday is gone for good! As an ex-systems administrator my life back in the good ol’ days was busy. Waiting for the next patches Testing the new patches Deploying the new patches …….. rolling back the new patches where it causes a legacy printer or other device to no longer function!…