#1, down and Dusty with Microsoft Sentinel. Sentinel is one of Microsofts Crown Jewels hidden so well in plain sight that many Managed Service Providers and cyber security teams do not even know it can help them significantly with investigating Indicators of Compromise or investigating a cyber attack to find the source and the target.
Security Information and Event Management (SIEM) products have been used by organisations for a long time, some of the traditional vendors include: Splunk and LogRhythm and there are many more. Initially these tools were used for application performance management and monitoring but over time the cyber security use case has grown an become the #1 reason for SIEM.
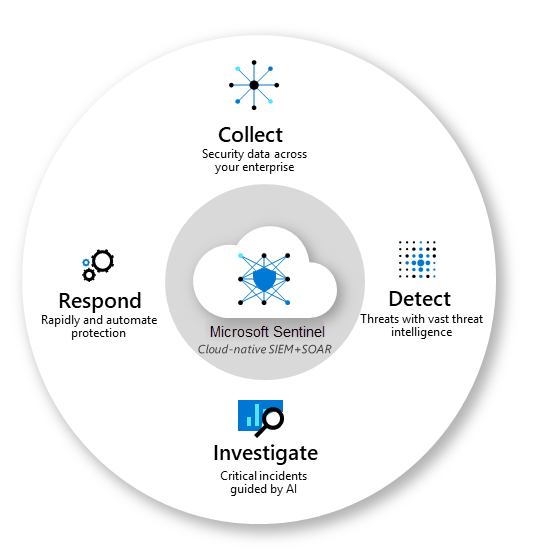
Today we will not cover SOAR (Security Orchestration Automation Response) as it is a vast topic in itself, but suffice to say that Sentinel with the integrations Microsoft has built is an extremely powerful tool.
For MSP’s who wish to extend your offerings, a Managed Microsoft Sentinel platform could be your method to do this, if you have clients who are required to keep the log data for compliance/audit/security reasons then Sentinel is an easy to learn and completely integrated with the applications your clients are using already, making it an easy starting point for a new service to offer your clients.
Intellectual property gives your business a competitive advantage, as it is difficult for other MSPs to replicate what you create. Therefore consider building a platform around offerings such as Microsoft Sentinel.
If you do not need the introduction then please go directly to the Microsoft Sentinel Brain dump, I speak with MSPs and end customers daily about Microsoft Sentinel and I want to share what I have found out through my interactions.
Introduction to Microsoft Sentinel
Microsoft Sentinel is a Security Information and Event Management solution (SIEM) alongside a Security Orchestration, Automation and Response (SOAR) platform and provides a platform for Threat hunting, Intelligent Analytics and Threat response.
Microsoft has a good description here of Sentinel and SIEM / SOAR, so I will refrain from repeating what the vendor can say much better than I can!
Typically conversations that start to extend to SIEM/SOAR are where industry needs certain accreditations such as ISO 27001 which requires an organisation to store log data read only for an extended period of time from all application, endpoint, identity sources etc and ISO 27001.
Equally though organisations who are serious about their cyber resilience programmes are investigating Security Information Event management solutions already as these solutions are the only way with the current capabilities in Machine Learning and Artificial Intelligence to present the data to human experts where breaches and attempts at breaches can be fully understood and investigated.
| 4. Mitigation strategies to detect cyber security incidents and respond | Risk | Microsoft option |
| Continuous incident detection and response | Compromise/Breach | Microsoft Sentinel, Graph API, Azure ARC |
| Host-based intrusion detection/prevention system | Compromise/Breach | Microsoft Defender for Business, Defender for Endpoint P2(ASR) |
| Endpoint detection and response software | Compromise/Breach | Microsoft Defender for Business, Defender for Endpoint P2 |
| Hunt to discover incidents | Compromise/Breach | Microsoft Sentinel, Graph API, Azure ARC |
| Network-based intrusion detection/prevention system | Compromise/Breach | |
| Capture network traffic | Compromise/Breach |
The table above maps Microsoft Sentinel to the Australian Signals Directorate Essential 8 (ASD 8) for protecting Australian organisations from cyber crime.
Do you need Sentinel at all?
A very valuable piece of advice was once given to me and that was to evaluate, write down as a future budget decision, then re-evaluate at the time of you budget review and determine:
- did you need the tool?
- if you had used the product what would have been the value vs cost?
- can I afford to go without?
This I say because for many who are making a decision on any technology, the fact is that they probably do NOT need and can probably re-use what they have to cover the capability of the new solution.
If you are a small business without specific ISO 27001 or ISM requirements then you may find that the overhead of having someone to manage Sentinel may prove too much and the usefulness of a SIEM becomes underwhelming so consider the management required as a part of your decision making.
In the case of Microsoft Sentinel, Sentinel is an extremely powerful tool and has a good free tier for M365 clients and Defender for EndPoint Server users etc but, Did you know that Defender for 365 can cover for a a lot of what is required for Threat hunting and where the typical use case for Sentinel lies.
Another option can be to simply store the log data in Azure storage until the time that you need to access it and use an analytics tool to look through and analyse the signal data for Indicators of Compromise etc.
Down and Dusty with Sentinel – proceeding
Now that we have covered whether or not you need a SIEM, let us discuss some of the considerations in deploying Sentinel, it is the easiest tool to enable and can be up and running in minutes. There is though consideration to costs, ingestion and long term management that you must consider and we will cover below.
Microsoft Sentinel – Brain dump
The information provided below is what I refer to as a quick start, it may not be formatted perfectly but it is data that can be valuable if you are looking to start a practise around SIEM/SOAR and specifically Microsoft Sentinel in this case.
Setting up Microsoft Sentinel
As Microsoft Sentinel is a SaaS platform there is very little configuration to get started, from your Azure portal, here:
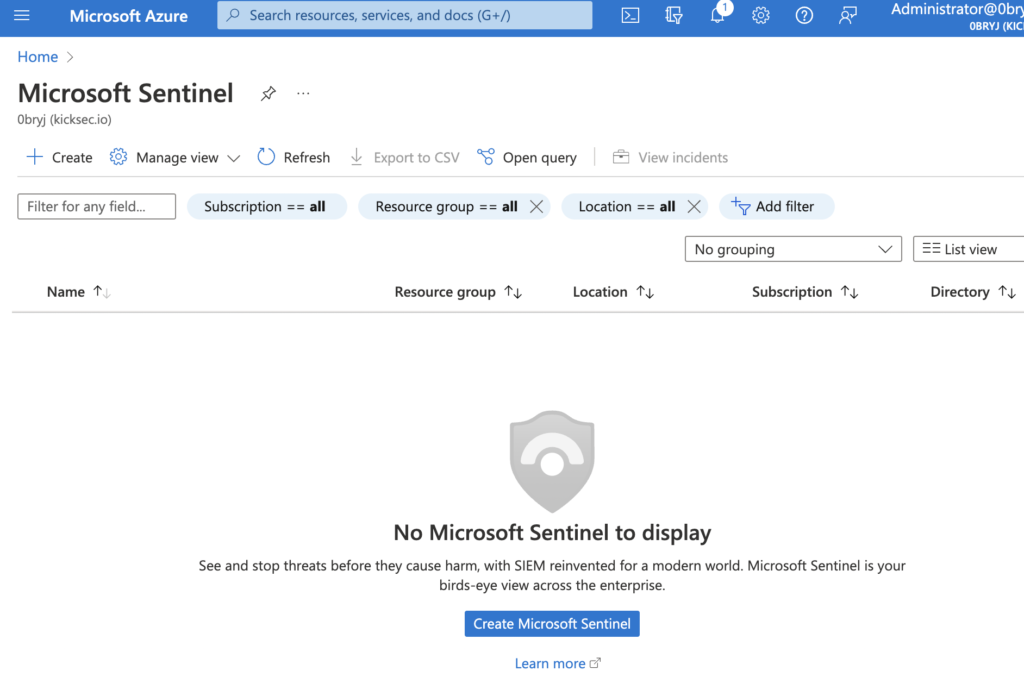
Initial Set up of Sentinel can be found here: as well as the full deployment requirements.
Microsoft Sentinel Training
I have found a couple of good sources for training and completing these, you become a guru, remember Kusto Query Language (KQL) – used T-SQL before, then you know KQL.
Microsoft sentinel documentation is here: Sentinel training part #1
For two part how to use microsoft sentinel there is more available below:
Microsoft has a library of pre built queries (Playbooks) and is also improving the Sentinel interface substantially with each passing month so you can now find a lot of low-code and no-code (KQL) ways to gain the insights that you need to drive Microsoft Sentinel.
Microsoft Sentinel importing log data
The importing of log data from Azure VMs is fairly straight forward as well, I used the following url to help with setting up connectors:
Connect Microsoft Sentinel to Azure, Windows, and Microsoft services | Microsoft Docs
As above for managing costs please review this link here.
When importing log data into sentinel review what method you are using as some from M365 sources have no cost when imported via Defender 365 for example but would have cost if imported in a different way. For each data type, review what data you need to retain and for how long you must retain it, avoid duplication of data and avoid storage of data that is irrelevant to your use case – storage (and paying for) is one area where there can be “Too much of a good thing” and it will bite you later on.
Microsoft Sentinel cost calculator
“How much is Microsoft Sentinel going to cost me”, this is a very common question I receive with my engagements. There is no tried and true answer to this, except that Microsoft provides some free ingestion of log data from other Microsoft platforms for 30 days, I believe this is around 500 MB per endpoint or identity from Microsoft Defender platforms such as Microsoft Defender for Endpoint P2 and Microsoft Defender for Office 365.
Considering the above, the best thing in my opinion to do would be to set a spend limit to start with, setting this cost very low will prevent a “bill shock” later down the track.
Warning: If Sentinel goes over its spend limit then log data will not be captured leading to “gaps” in your timeline. Be careful in a production environment to watch your spend limits.
Deploying Microsoft Sentinel Analytics Rules that are Already Enabled – Azure Cloud & AI Domain Blog
Estimating raw data ingestion from M365 into Sentinel, more information can be found here:
Here is another very good cost calculator:
Update a recent article I aggregated some further information on optimising Sentinel spend here. Microsoft Sentinel is an extremely powerful tool but make sure you are watching its growth to ensure that your organisation does not overspend to have the rich analytic data Sentinel can provide.
Azure Monitor agent overview – Azure Monitor | Microsoft Docs
And finally some further cost information on Microsoft Sentinel here:
https://azure.microsoft.com/pricing/details/monitor/
Microsoft Sentinel summary
There is an absolute plethora of data available regarding Microsoft sentinel, if you have corrections or wish to point me at other sources then please let me know. My goal with these articles are to upskill clients and MSPs with the technologies that we work with in our day to day roles.
I also have a goal of right sizing client costs and some of the cost reduction methods above will help you stay away from any bill shock.
Finally, where you need log gathering and storage via a SIEM but can not manage the solution then look to MSSPs or specialist providers who can assist with handling and being the SOC team with your sentinel data.