Welcome to mass Travel disruption!
Read More: Welcome to mass Travel disruption!The shape of things to come for Australians? ….. I am the worst at actually printing out a “Hard copy” of any ticketing or required material, I like to rely on Technology and use the apps on my phone…. It is guaranteed …… without a doubt that our “Vaccination Certificate” Covid Government app back-end infrastructure…
Work from home? hacking is cheap to start out in
Read More: Work from home? hacking is cheap to start out inComing back to what I have discussed before, it is really cheap to get started as a “Wannabe” haxxor…… just search Reddit for red teaming and join the groups for public “Proof of Concept” hacks for each new vulnerability as it is announced (seriously!) ……. There are two solutions to this, either may be suitable:…
Find a Vulnerability in Software, Get sued by Vendor
Read More: Find a Vulnerability in Software, Get sued by VendorBad form or what? Find a Vulnerability, notify the vendor, get sued! IMHO, many vulnerabilities are not published already, and this only makes it worse….. sell the vulnerability on the Dark Web = profit. Let the Vendor know about it ….. get punished? Reason #233 for having a Cyber Security plan in place to protect…
When Smart locks are too smart!
Read More: When Smart locks are too smart!larger than the problem itself?
You will be Attacked! What do you do?
Read More: You will be Attacked! What do you do?Cyber Security is a necessary part of your operation, no Cyber Security plan places your business at risk of being ruined, unlike traditional theft where a criminal needs to breach your physical office location. A Cyber Security attack from criminals is targeted across as many businesses as they can reach, searching for an easy victim,…
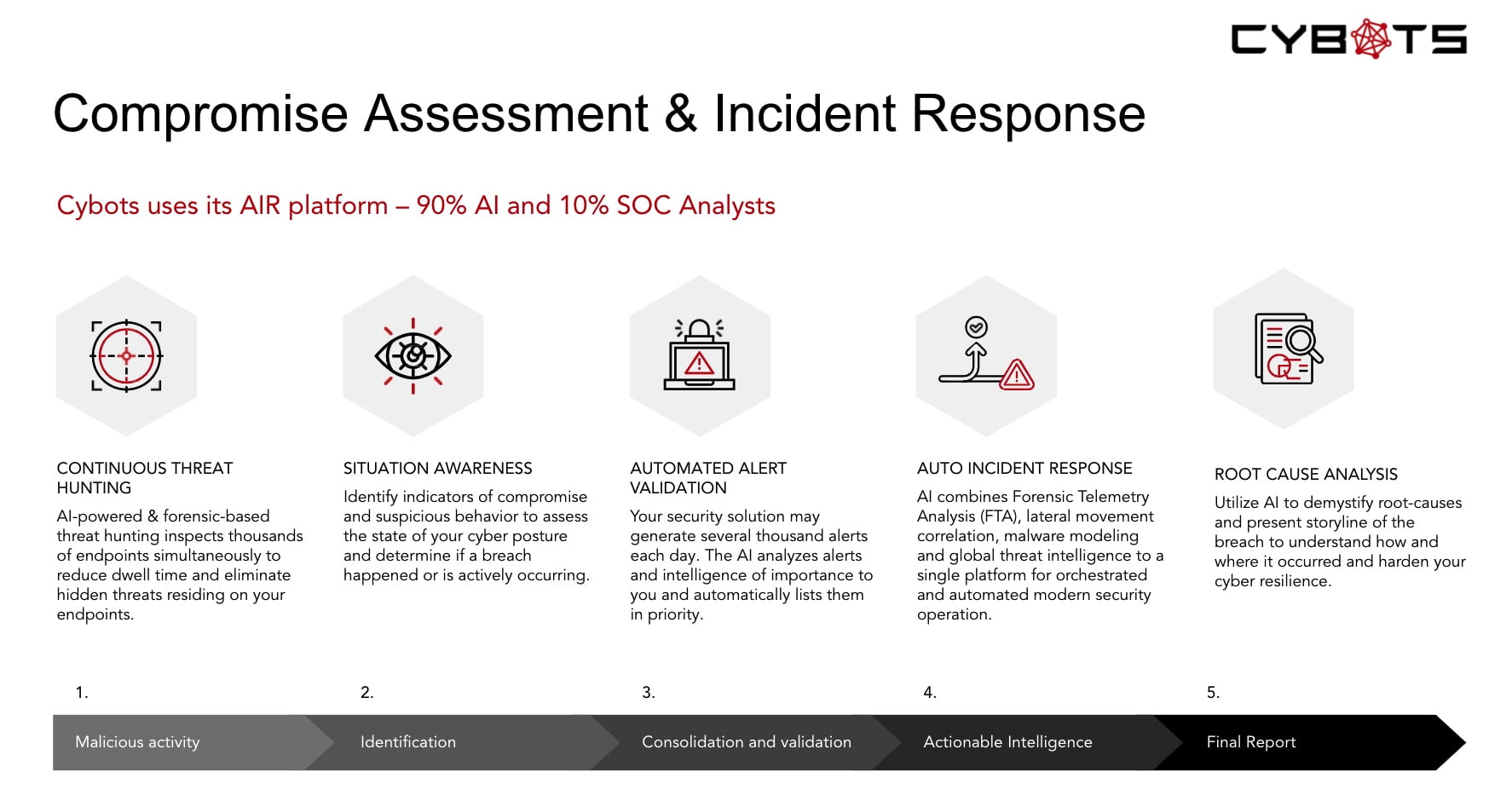
Artificial Intelligence?
Read More: Artificial Intelligence?Artificial Intelligence is not always Artificial Intelligence, every Cyber Security vendor selling solutions today is either putting an “using AI” sticker on their website, or they are investigating how they can use Artificial Intelligence “AI” and Machine Learning “ML”in their branding. It stands to reason as the terms are well on the incline of the…
Help! choose a vendor
Read More: Help! choose a vendorIn the Cyber Security industry there are no sure bets, large companies have revenue and legacy products to protect, which stifles innovation.
Insecure – MicroSoft Autodiscover
Read More: Insecure – MicroSoft AutodiscoverMicrosoft Exchange servers autodiscover function, configured by the wrong hands, is not secure! A systems administrator who incorrectly sets up their on-premise Autodiscover record could be assisting miscreants to slurp up credentials from an organisations users trying to connect to their corporate email account.
The cost of SSO?
Read More: The cost of SSO?A friend of mine recently posted this interesting article on adding Single Sign On for various vendor products (thank you Charles) and I wanted to share, primarily because it gives an insight into the ways that some vendors are gouging their customers for functionality that has a negligible cost for the vendor and in some…