Data Sovereignty and AI
Read More: Data Sovereignty and AIData Sovereignty and AI – The reason why it is so extremely important to perform 3rd party supplier audits is not a secret, even if you have the most impervious security controls known to humanity it means zero when your providers do not have the same security first mindset. The Australian Government may just have…
Agents are everywhere (AI)
Read More: Agents are everywhere (AI)Agents are everywhere (AI), Claude agents are SO amazing! equally OpenClaw is really cool, both of these “cool” technologies are being used in businesses all over the world right now. Ask the next time you are engaged with one of your clients or they will say to you “we are going to sign up for…
The Cyber Security ‘Market’ and AI
Read More: The Cyber Security ‘Market’ and AIThe Cyber Security ‘Market’ and AI, these introductions to new hires make my spider senses go haywire! These CRN posts always make me cringe, a ‘supposed’ subject matter expert (definitely NOT) is interviewed and provides their ‘Advice’ on where the market is going. I am not calling out Shabeel Shah individually here but rather the…
Product enshittification
Read More: Product enshittificationProduct enshittification has been underway for a few years now, the Norwegians have captured this in such a powerful yet humorous way in this video. Software Enshittification: Once you have a Popular product, maximise revenue per line item, lock important features (like basic security) away with a tier upgrade, buy the startups who compete and…
Anthropic Security Agents will change the Managed Security Operations game forever
Read More: Anthropic Security Agents will change the Managed Security Operations game foreverAnthropic Security Agents will change the Managed Security Operations game forever. Anthropic just dropped a MDR / Managed SOC bomb that looks like it is the real deal, causing an immediate stock price drop across the major cyber security companies globally, arguably more of a “true up” than a valuation change as it is the…
It’s not you, Generative AI is making you dumber
Read More: It’s not you, Generative AI is making you dumberIt’s not you, Generative AI is making you dumber.
The Holland Foundation – Melbourne
Read More: The Holland Foundation – MelbourneThe Holland Foundation – Melbourne https://hf.org.au Be very very careful of this organisation and their 5 star reviews, my daughter started ‘working’ (no pay, that’s ok it was a volunteer role) for the foundation several months ago, before she started they insisted that she should pay a $150-200 deposit to be shortlisted into a role,…
Microsoft M365 E3 now includes – Defender for Office 365 Plan 1
Read More: Microsoft M365 E3 now includes – Defender for Office 365 Plan 1Microsoft M365 E3 now includes – Defender for Office 365 Plan 1 If you have M365 E3 licenses in your business, you now have the added benefit of Defender for Office 365 Plan 1 included; securing your Email, Teams, Sharepoint and Onedrive from advanced threats. From July 1st 2026, MDO (Microsoft Defender for Office 365…
AI wheels falling off? Microslop – can not help it!
Read More: AI wheels falling off? Microslop – can not help it!AI wheels falling off? Microslop – can not help it! This is not about Microsoft, Microsofts; CEO Sataya just happened to make a statement last week, which was not well received for well founded reasons! Personal opinion piece I don’t know what everyones take on the current hype around AI or Artificial Intelligence is but…
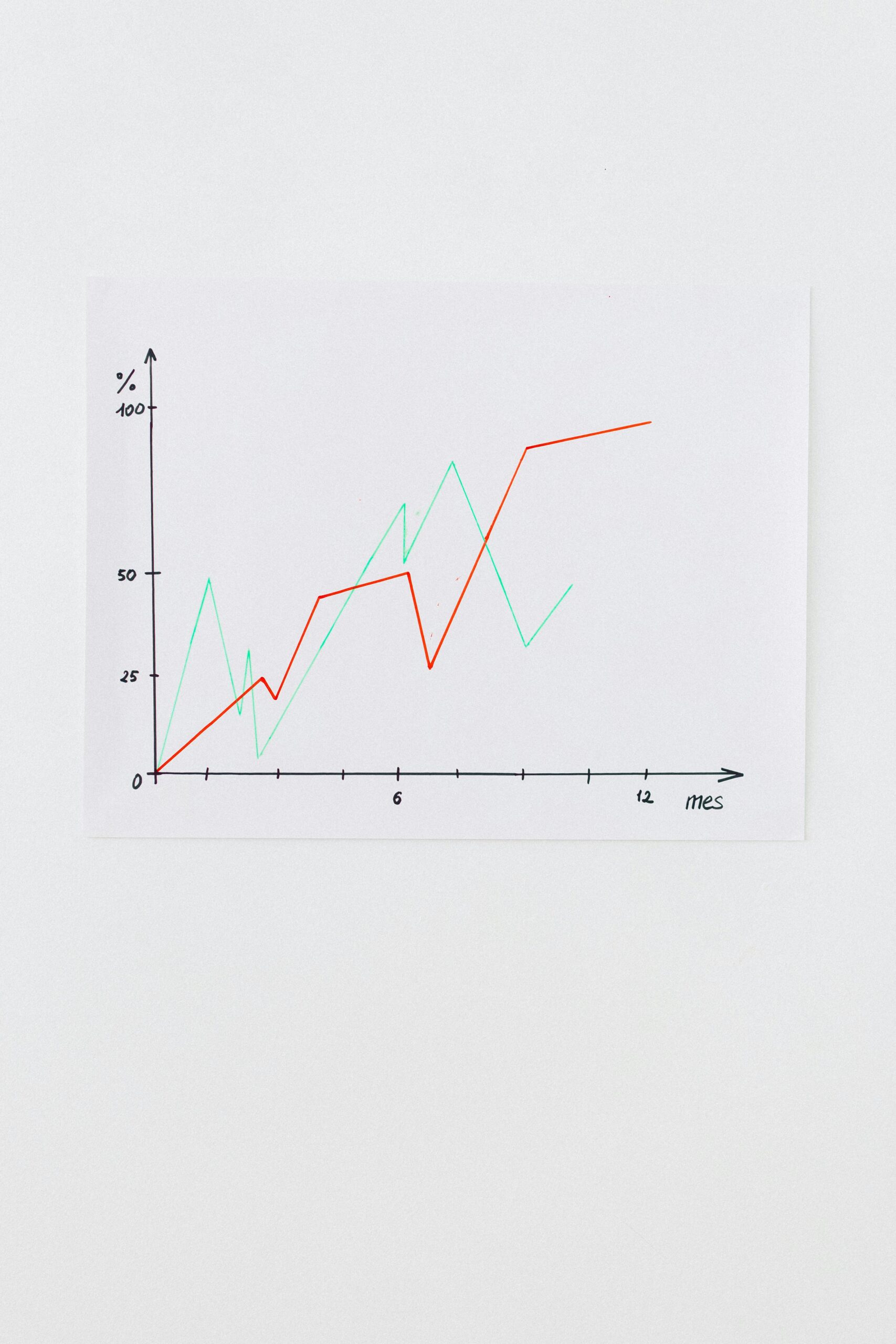
Is AI Profitable?
Read More: Is AI Profitable?Is AI Profitable? Very interesting opinion on AI ‘wrapper’ apps, by extension this also applies to the underlying AI company business models, losing money is not a sustainable business practise and most use cases for AI are not job replacing, nor are they money making ever. Solving boring business problems is where there is a…