Small to Mid enterprise companies in Australia are extremely vulnerable to revenue disruption and most likely financial disaster from cyber breach – Auto parts importer lost $880k 2 months ago as an example, not the typical target for a cyber criminal, or is it?
Yesterday in one Risk Intelligence report we ran for a client we found that their suppliers: a Curtain importer, and GPS shop and small Australian Software developer developing middleware for industry had been breached and many email addresses and passwords were in clear text and being actively sold on the Dark web.
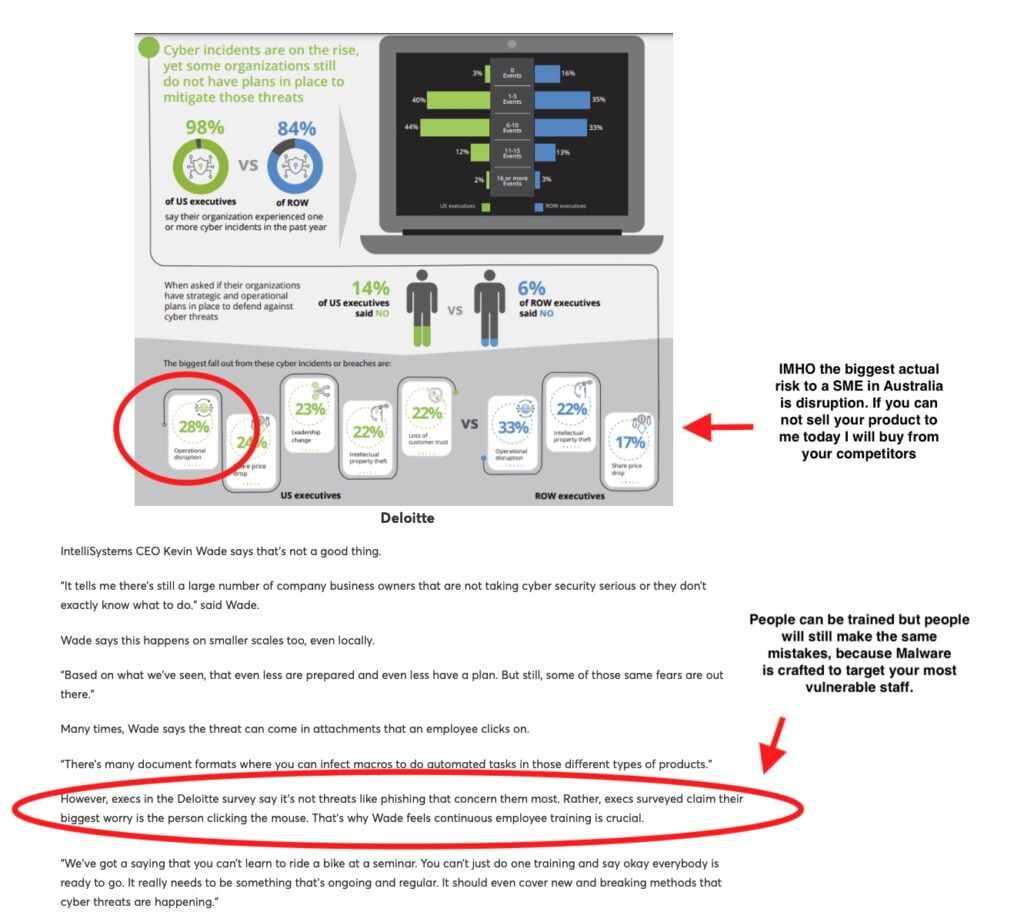
Teaching your staff to not open emails that are not from known sources is critical.
This does not stop malware, because you are not your most vulnerable staff member, neither does Anti Virus software.
Active controls need to be in place that look for malicious activity such as: Privilege use, Powershell use, certain exe’s, UEBA “Tells” etc. This is typically End Point Detection and Response (EDR), eXtended Detection and Response(XDR) and Advanced Managed Detection and Response (AMDR).