Introduction
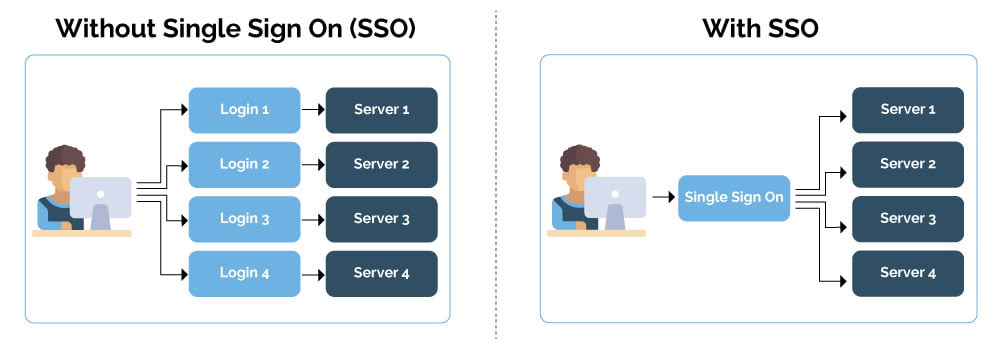
Single sign on (SSO) is an authentication method where accessing different systems and applications uses a single set of credentials, that credential is able to be used by each system querying a central system (Authentication service) to provide the user access to a service or system. This is different from a Password manager or “Screen Scraping” where a user name and password is “replayed” into the session.
An example of Single Sign on is your Facebook or Google Account being used to connect you to third party platforms and services as happens with games and services today. The Third party system/service you requested access to does not ever know your Facebook or Google password – instead a token is provided to the third party platform with the assertion that you are who you say you are because the authenticator (Facebook or Google) trusts you.
The protocols that you may see used with Single Sign On are: OAuth, SAML or OpenID which all provide broadly the same functions.
Single sign-on example
You might find that description a bit abstract. Let’s look at a specific implementation example to see how SSO works in practice. Imagine you’re the user in an environment with single sign-on and you’re trying to get access to some resource on a server. The sequence of events goes like this:
1
You attempt to access the service provider—again, this generally is an application or website you want to access.
2
As part of a request to authenticate the user, the service provider sends a token that contains some information about you, like your email address, to the identity provider, a role played by your SSO system.
3
The identity provider first checks to see whether you’ve already been authenticated, in which case it will grant you access to the service provider application and skip to step 5.
4
If you haven’t logged in, you’ll be prompted to do so by providing whatever credentials the identity provider requests.
5
Once these credentials have been validated, the identity provider will send a token back to the service provider, confirming that it’s authenticated you.
6
This token is passed through your browser to the service provider.
7
Once received, the token is validated according to the trust relationship that was set up between the service provider and the identity provider during the initial configuration.
8
The user is granted access to the service provider.
https://www.csoonline.com/author/Josh-Fruhlinger/
Benefit: Single Sign On (SSO) reduces password complexity, reducing password complexity helps stop users from sticking their passwords on their monitors. SSO also is a first step toward being able to audit the: Who, What and When of user access to corporate systems and data.
Note: When an older/or not supported platform is connected to “Single Sign On” services there is often a go between process of “Screen Scraping” or text entry occurring using a client based tool and this is often called: “Simplified Sign On”
How does Single Sign On stop me being hacked?
The benefits of Single Sign On are more indirect than direct benefit when referring to Cyber Security. Single Sign on has the following benefits from a Cyber maturity perspective:
- Managing credentials centrally is best practise whether using an Identity Management platform or manually managing your Directory service.
- Having a single credential ensures that auditing where a user has authenticated is easier to report on
- A single credential means a single password to remember, multiple passwords and out of sync password policies lead to issues with password security
- It is easier to include Multi factor authentication where the authenticator is a single plaform
- When decommissioning a user it is easier to completely deprovision when there is only one account to remove, as opposed to credentials being stored on individual machines.
https://en.wikipedia.org/wiki/Single_sign-on
Please leave a comment if there is anything you would like to add to this list?




