101: Basic Security Posture for WordPress, WordPress is one of the most popular internet technologies in use today, as a tool for amateur and professionals wanting to blog, to sell, to consult or to do almost anything else, nothing comes close to the WordPress ecosystem for flexibility and extensibility – want to build a store front, no problems, want to build an educational site – easily achieved.
With great power though comes great responsibility or risk, WordPress being the platform that it has come to be is subject to large numbers of threats and vulnerabilities, the latest vulnerability announced here from this past week in January 2023.
Another from late December 2022 Linux malware affects WordPress just goes to demonstrate how active cyber criminals are with their activities around WordPress as an attack vector or as a ransomware target.
There are some simple Security Posture related activities that you can undertake as the site admin to ensure that your WordPress instance is: As Secure as Practical (ASAP) and will be recoverable in the unfortunate case that you are still the victim of a cyber attack.
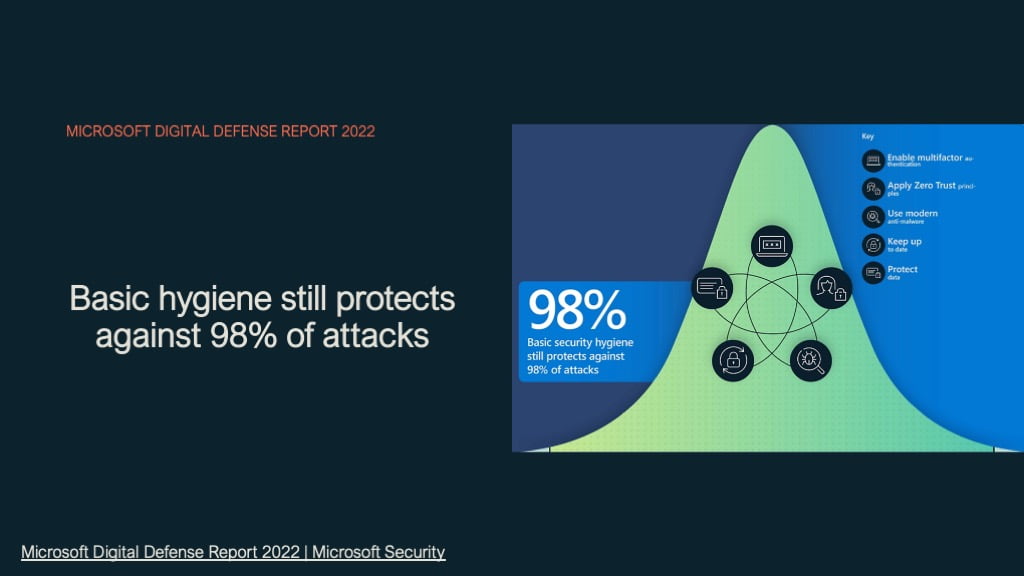
There is no way to be 100% secure but good security posture prevents most cyber crimes and discourages criminals looking to compromise your organisation.
Basic security Posture for WP – steps
So how to prevent malware attacks on WordPress websites, let us go into some considerations for the mitigations that are easiest to implement yet provide the most benefit.
- Backup, backup and backup again your WordPress sites, how regularly you update the content or changes occur should be the benchmark for your backups. For example a storefront transacting 100s of items per day must be backing up as frequently as every few minutes to every hour. Whereas a blog site such as Kicksec.io can get away with backups once a day because the content is not changing as regularly.
- Hourly backups should be easily accessible, daily backups also. But have at least one daily backup that is not stored on the same WordPress instance and can not be modified by the Backup plugin or the poster you are using – in other words have it stored/copied to another location.
- Use Multifactor Authentication where possible for your daily login especially if your WordPress site is business critical, if you can not use MFA then use a complex passphrase of more than 12 characters and uppercase/non-alpha and numbers.
- Your WordPress admin account should not be secured using Multifactor authentication as you may need to access this login when your MFA provider is unavailable so this account password should be complex and stored away in a secure password manager – possibly not Lastpass! This Account should not be used except in emergencies
- Use the model of least Privilege for roles within WordPress, for your daily blog posts configure yourself an account that only has the necessary rights to manage posts – possibly Editor or Author and use this for your daily activities with a different password to your administrative account for managing plug-ins and modifying your WordPress site settings.
- Youtube video on Managing access
- Implementing the least privilege model for WordPress
- Minimise Plug-in use, every plugin that you add to your WordPress instance adds a possible vulnerability. Plugins and even “full fat” vendor software is most often built with security as an afterthought, or no thought at all – always assume this to be the case with any software or plugin and consider any third party plugin seriously for necessity before implementing – it is often impractical to check everything for a blog site but where your WordPress instance is business critical then you must fully investigate every single plug-in or add-on.
- Is the vendor well known, do they have a good history and good reviews
- Can I do what this plugin does with an existing plugin or an add-on from an existing plugin provider I am using?
- What does this plugin do, what permissions does it need and what does it change on my WordPress site.
- Most of all, WordPress plugins slow down your Response times and create other potential issues with your WordPress instance – so avoid as much as possible
- Patch and update WordPress regularly, ensure that your WordPress instance is set to update WordPress itself and plugins at least every 24 hours. A potential cyber criminal can find your WordPress instance in 30 seconds with a google search looking for a particular website response – it is trivial for an attacker to find a vulnerability without considering a dark web search that has 1000s of times more data specific to vulnerabilities.
- Use an external identity provider for users using your service, there are many plugins to allow users to login using their Facebook/google/twitter or other O-Auth provider to authenticate against your WordPress site if this is required. This gives you a couple of advantages:
- The identity of the user connecting to your instance is verified by another platform and they have better checks and balances on who this identity belongs to.
- You have outsourced the identity management of your users to their own Identity Provider (IDP), no password changes etc to manage
- WordPress uploads folder access open to public, for most admins this is ok as the uploads folder contains your images etc for your site. If on the other hand your uploads folder contains docs, videos, presentations etc that should be behind a login then you must ensure that this folder is secure and not accessible to Public, I have linked an article here to disable public access to the uploads folder.
- Use a Caching service such as Cloudflare to protect your content from DDOS and other attacks as well as give your site a super speed up at the same time. For smaller WordPress sites this service from Cloudflare is free to use.
- Remember to clear the cache when you are making changes to your WordPress site when you are using any cache provider.
Summary – Basic Security Posture for WP
The above security posture principles are not only useful for securing your platform they also follow the Zero Trust Network Architecture:
- Verify Explicitly – Use Multi Factor Authentication for WP
- Least Privilege – define roles within WP for staff and utilise an external Identity provider for guests where possible
- Assume Breach – Patch and update always, use the least number of WP plugins
WordPress sites are an attack vector for cyber criminals, the only reason we do not read about them is that the majority of WordPress users are small business and do not make enough noise to be noticed, unfortunately for a small business having their WordPress based shop front out of action could be crippling or business fatal.
As always please reach out if I can assist in any way to help secure you or provide you with additional advice and assistance here or email: [email protected]





2 responses
[…] Multi-factor Authentication, as a security control it is one of the most basic yet necessary controls and must be fully implemented in order to reduce the risk and possible extent of a compromise. […]
As always I am seeking advice and further insights on securing platforms including WordPress, please feel free to leave your comments.