Link is at the bottom of this article, the NZ Cert document is very well written and I recommend you read it and implement the steps within. For these sorts of attacks an EDR tool or an MDR provider will help immensely in understanding what is occurring at the time of a ransomware attack.
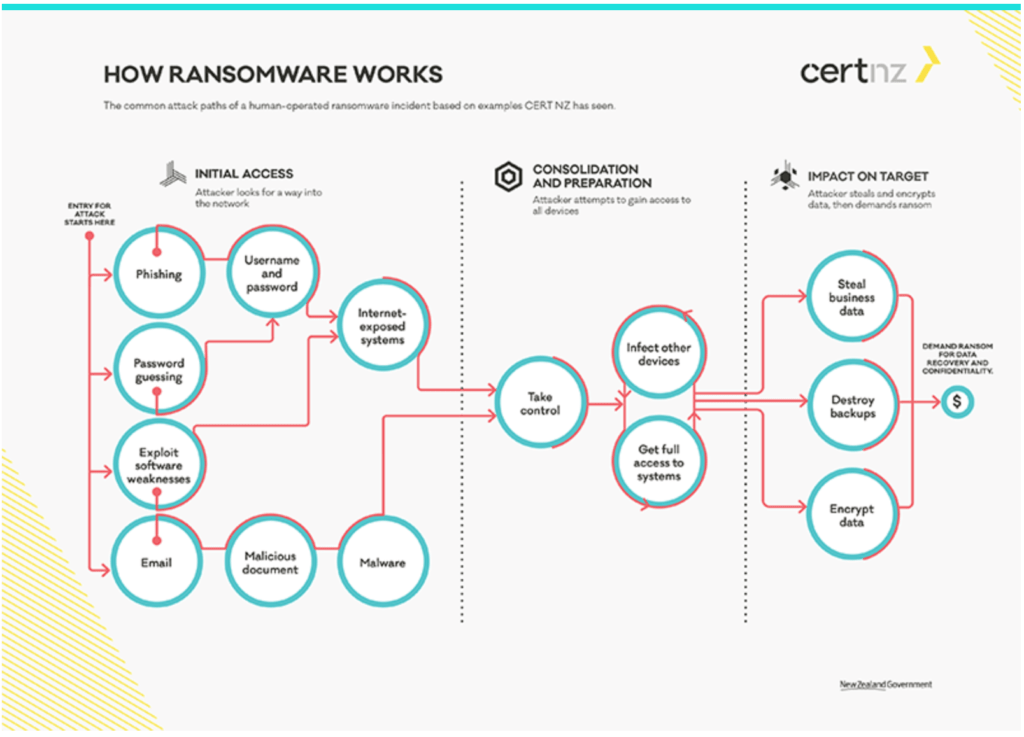
Ransomware at its most basic prevents a user or an organisation from accessing their data. The attacker will often have accessed the system through Phishing and will encrypt the data that they can access within, if they have not been able to move too far laterally then the incident may be fairly isolated. By Encrypting the data the “Data Owner” loses access to the information without the encryption key, which only the attacker knows.
Most times there is no way to recover data that has been encrypted without the key and the Attacker relies on this fact to request a Ransom paid via an anonymous means like Bitcoin.
A ransom should never be paid to attackers, there are a few reasons why:
- There is no guarantee that the attacker will give you the encryption key, you lose your money and your data
- By paying an attacker you only increase their Boldness in the future
- With a carefully pre planned strategy you will be able to recover your data with minimal downtime
To minimise the risk of being a target there are a few things you should do, even without advanced tools and Cyber Security systems to help, you can still be mostly secure.
- Training your users first, What should they do if they are asked for a password by an app? what happens when an email is received and asks for their details? etc
- Make sure that your users have access to the data they need to do their jobs only. Make users responsible for auditing their own access and set sensible Access Control Rights across your systems.
- Implement Multifactor authentication for all platforms and systems that have sensitive data or data that your business needs to operate, the more sensitive the data, the more secure you must make access to it.
- Ensure that you have a backup of all data and in more than one location incase of disaster, whether cold standby, snapshots, full backups etc.
- Most importantly: Build a plan with the teams that will be responsible for the recovery of data after a ransomware attack has occurred.
- Emergency team
- Contact details
- Executive sponsor
- Communication plan if that is the system attacked
- How to identify the ingress point of the breach and block before recovering (are there agents still running, how did the attack happen).
- The list of systems/services to include in the list, with criticality of each and recovery order.
- Whether to restore/rebuild or build again
- How to recover the each platform, who is responsible
- Restore
- Communication with users and if necessary customers
- Finishing up
- Obtain executive sponsorship for the plan and then implement (do not store in only one place incase the plan is locked up by Ransomware too!)
- Test the plan, every month: Test the process and test that you can recover data from your backups
And remember that when an incident does happen you can recover the data, it is unlikely to be all systems and with a plan you can restore the data in what ever order is deemed most important.
At the time of incident it will seem overwhelming, but have a plan and your team will be best prepared to recover quickly and with the least downtime.
https://www.cert.govt.nz/business/guides/protecting-from-ransomware/



